Beyond Legal #35: The supply chain manager who thought sub-processors were someone else's problem
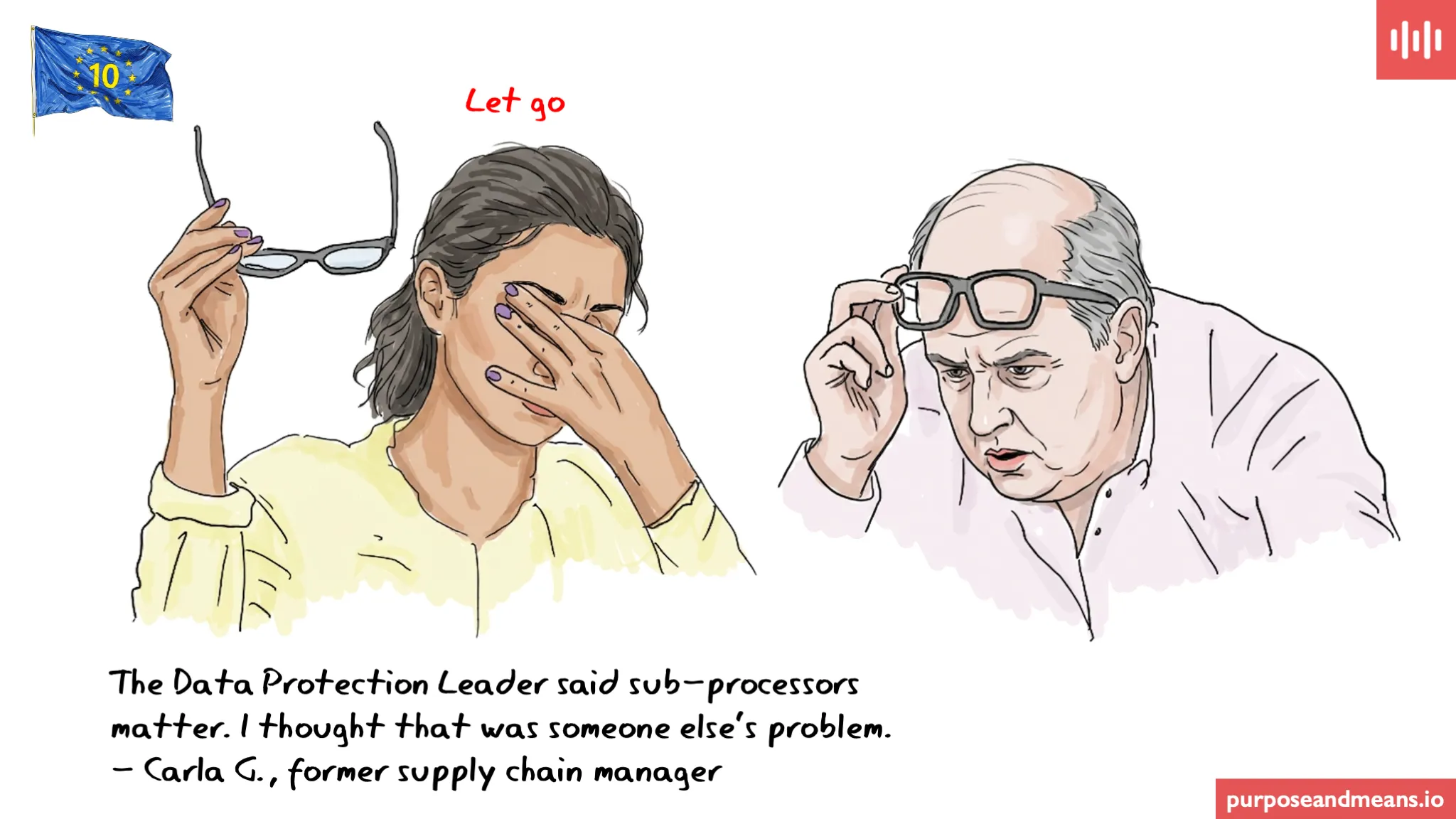
The Data Protection Leader said sub-processors matter. I thought that was someone else’s problem. — Carla G., former supply chain manager
Sub-processors are one of the most consistently underestimated risks in companies, large and small. The controller has a data processing agreement (DPA) with a logistics company. The logistics company uses a fulfilment platform. The fulfilment platform uses a last-mile delivery partner. The last-mile delivery partner uses a route optimisation tool. At each link in that chain, personal data — could be customer names, addresses, delivery instructions, sometimes more — are being processed by an entity the controller has never assessed, never contracted with, and in some cases never heard of. Under the GDPR, the controller is accountable for all of it.
Sub-processor governance was one of the most consistently underestimated practical obligations when the GDPR came into force in May 2018. The text of Article 28 was clear enough. What took longer to land — in boardrooms, in procurement teams, and in supply chain functions — was that the obligation was operational, not contractual. Having a DPA in place was never the point. Knowing what was happening beneath it was. Ten years of enforcement have progressively confirmed that regulators understand the difference, even when controllers do not.
Carla’s story #
Carla is a supply chain manager at a European consumer goods company that ships directly to customers across twelve EU member states. Her job is to get products to customers efficiently — managing carrier relationships, negotiating fulfilment contracts, monitoring delivery performance, and solving the operational problems that arise when things go wrong in transit.
She is good at it. She thinks in terms of delivery windows, cost per shipment, and carrier reliability. Unfortunately, she does not think in terms of processing activities, sub-processor chains, or controller accountability — and nobody had ever suggested that she should.
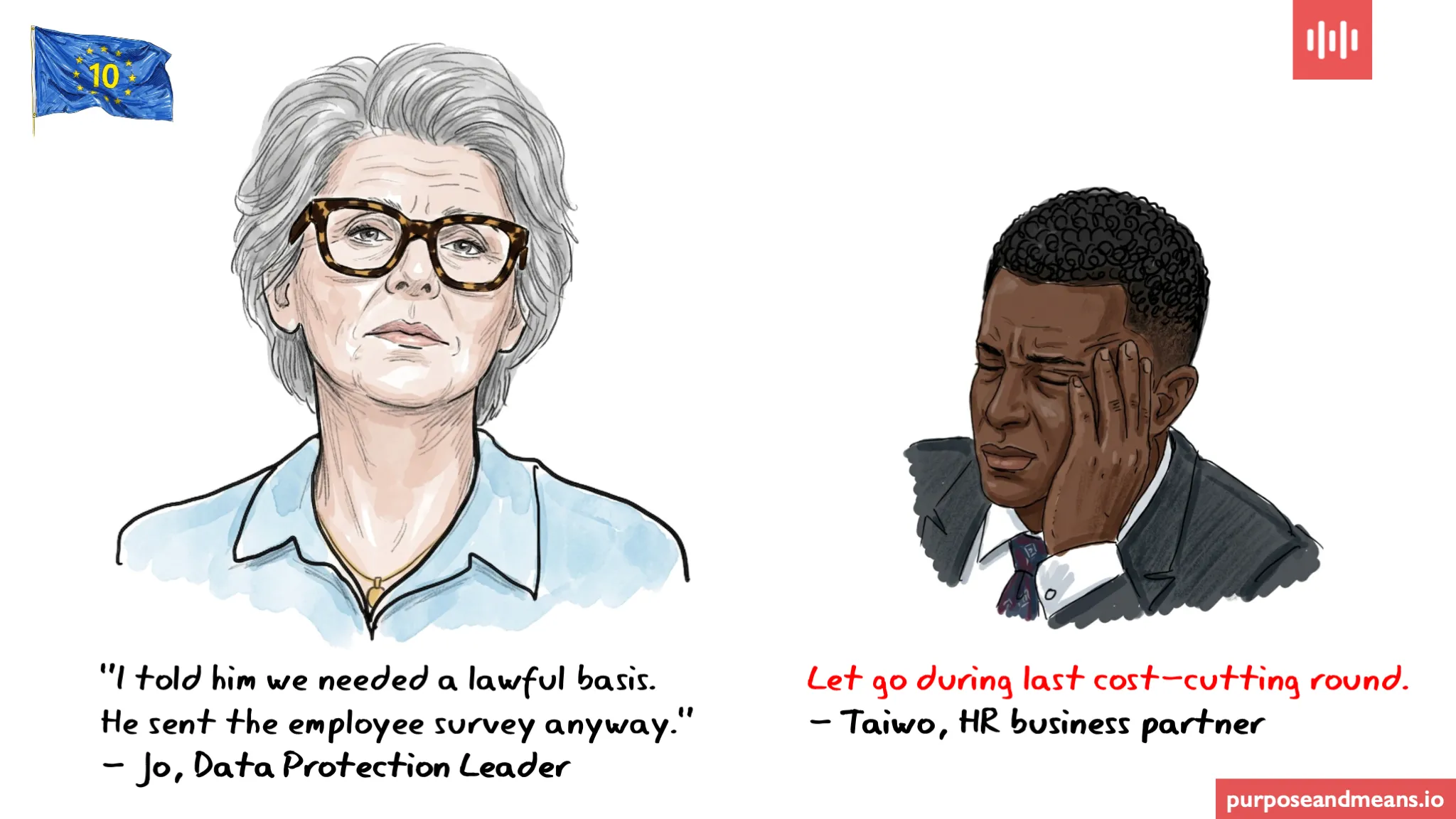
The Data Protection Leader — let’s call him Daan — had been trying to get visibility into the company’s logistics data flows for several months. Every time he approached the supply chain team, the answer was the same: we use contracted carriers, they are in the vendor system, procurement handles the agreements. What he could not get was a list of the sub-processors those carriers used, or any confirmation that the carriers were contractually obliged to notify the company before engaging sub-processors who would have access to customer data.
When Daan eventually got access to the carrier agreements, what he found was not a managed sub-processor chain. It was a series of standard logistics contracts with no Article 28 language, no sub-processor notification clauses, and no restriction on the carriers’ ability to pass customer data to downstream partners without the controller’s knowledge or consent.
What the audit revealed #
Daan’s mapping exercise identified seven tiers of data processing that the controller had no visibility into, covering the personal data of over three million customers. Two of the sub-processors at the third tier were operating in countries without an adequacy decision, without standard contractual clauses. This was not merely an extension of the sub-processor governance problem — it was a separate and concurrent violation of Chapter V of the GDPR, which restricts the transfer of personal data to third countries regardless of whether the transfer occurs at the first tier of processing or the fifth. The two failures are connected but distinct, and both require remediation in their own right. One had experienced a data breach two years earlier that the controller had never been notified of, because there was no contractual mechanism requiring notification.
Carla had not known any of this. She had done her job as she understood it. The problem was that her understanding of her job did not include the data protection implications of the vendor relationships she was managing.
Daan escalated to the board. A remediation programme was initiated. Carla was made redundant as part of a restructuring that combined the supply chain and data governance functions under a single accountable director. The decision reflected something more significant than a cost-saving measure. The board’s view was that the separation of those two functions had itself been a structural risk — that as long as the person managing carrier relationships and the person responsible for data governance were operating in different reporting lines with no shared accountability, the gap that Daan had uncovered was always going to exist. The restructuring was an acknowledgement that vendor relationships involving personal data cannot be managed by someone who has no data protection accountability, and cannot be overseen by someone who has no operational visibility into how those relationships actually work.
What does the GDPR require from controllers when processors engage sub-processors? #
Under Article 28(2) of the GDPR, a processor must not engage another processor — a sub-processor — without the prior specific or general written authorisation of the controller. Where general authorisation is given, the processor must inform the controller of any intended changes concerning the addition or replacement of sub-processors, giving the controller the opportunity to object. In practice, general authorisation is only a compliant mechanism if the notification and objection process it depends on is genuinely operational. A clause in a DPA that requires the processor to notify the controller of sub-processor changes is worthless if the notifications are never sent, never received, or received and filed without review. Controllers who rely on general authorisation need to verify not only that the contractual mechanism exists, but that it functions — that notifications are routed to someone with the authority and the knowledge to assess them, and that the controller’s right to object can be exercised in time to matter.
The processor must also impose the same data protection obligations on the sub-processor as are contained in the controller-processor agreement, by way of a written contract. If the sub-processor fails to fulfil its obligations, the processor remains liable to the controller for the sub-processor’s performance.
Two enforcement decisions show what happens when this chain breaks down in practice. In 2021, the Spanish Data Protection Authority (AEPD) fined Vodafone Spain €8.15 million — a record fine for Spain at the time — in part because the company had outsourced its telemarketing operations to third parties without maintaining any real, continuous, or audited control over how customer data was being used by those parties. The AEPD found that Vodafone Spain was operating without any means to verify the origin or legality of the data being processed by its contractors, and without documentation sufficient to demonstrate compliance with its controller obligations. The violations spanned multiple GDPR provisions, including failures of lawful processing and data subject rights, with the sub-processor governance failures forming part of a broader pattern of non-compliance.
In another case, this time in February 2024, Italy’s Garante fined Enel Energia €79.1 million after an investigation found that the company had acquired contracts from sales agencies that had obtained customer data through illicit means, that its systems had allowed unauthorised agents to access and process customer data for years, and that Enel as controller had failed to implement the technical and organisational controls necessary to govern what was happening within its extended processing chain. The violations in that case engaged Article 83(5) grounds — including failures under Article 5 and Articles 24 and 25 — reflecting that the breakdown was not limited to processor governance but extended to the company’s fundamental accountability and data protection by design obligations. In both cases, the company had processor relationships. What it did not have was visibility into, or control over, what those processors were doing with the personal data they had been given.
What does Article 28 require from a supply chain manager? #
The controller’s obligations under Article 28 of the GDPR do not stop at the first processor in the chain. They extend, through the processor agreement, to every sub-processor that has access to personal data in connection with the controller’s processing activities. For a supply chain manager, this means three things that are operational, not legal. First, every vendor contract involving personal data must include Article 28-compliant terms — not standard logistics language, but specific data protection obligations covering sub-processor authorisation, notification of changes, and liability. Second, the company must maintain visibility into the sub-processor chain below each processor — not just who the carrier is, but who the carrier uses, and what data those parties can access. Third, any change in the sub-processor chain that involves a new party accessing customer data must be authorised by the controller before it happens, not discovered after. Fourth, the sub-processor chain must be reflected in the company’s Records of Processing Activities under Article 30. In practice, the RoPA is one of the most reliable diagnostic tools available: if a supply chain manager cannot complete an accurate RoPA entry for a logistics processing activity — because they cannot name the processors and sub-processors involved, or describe what data each party receives — that gap is not a record-keeping problem. It is evidence that the processing itself is not under adequate control.
A supply chain manager who does not know which sub-processors are handling customer data is not managing a risk that is someone else’s problem. They are creating a risk that will eventually become the controller’s.
The challenge for today: Take your three largest logistics or fulfilment carrier contracts and ask one question: does each contract restrict the carrier from engaging sub-processors who will have access to customer personal data without your prior authorisation? If the answer is no, or if you need time to find out, you have found the gap.
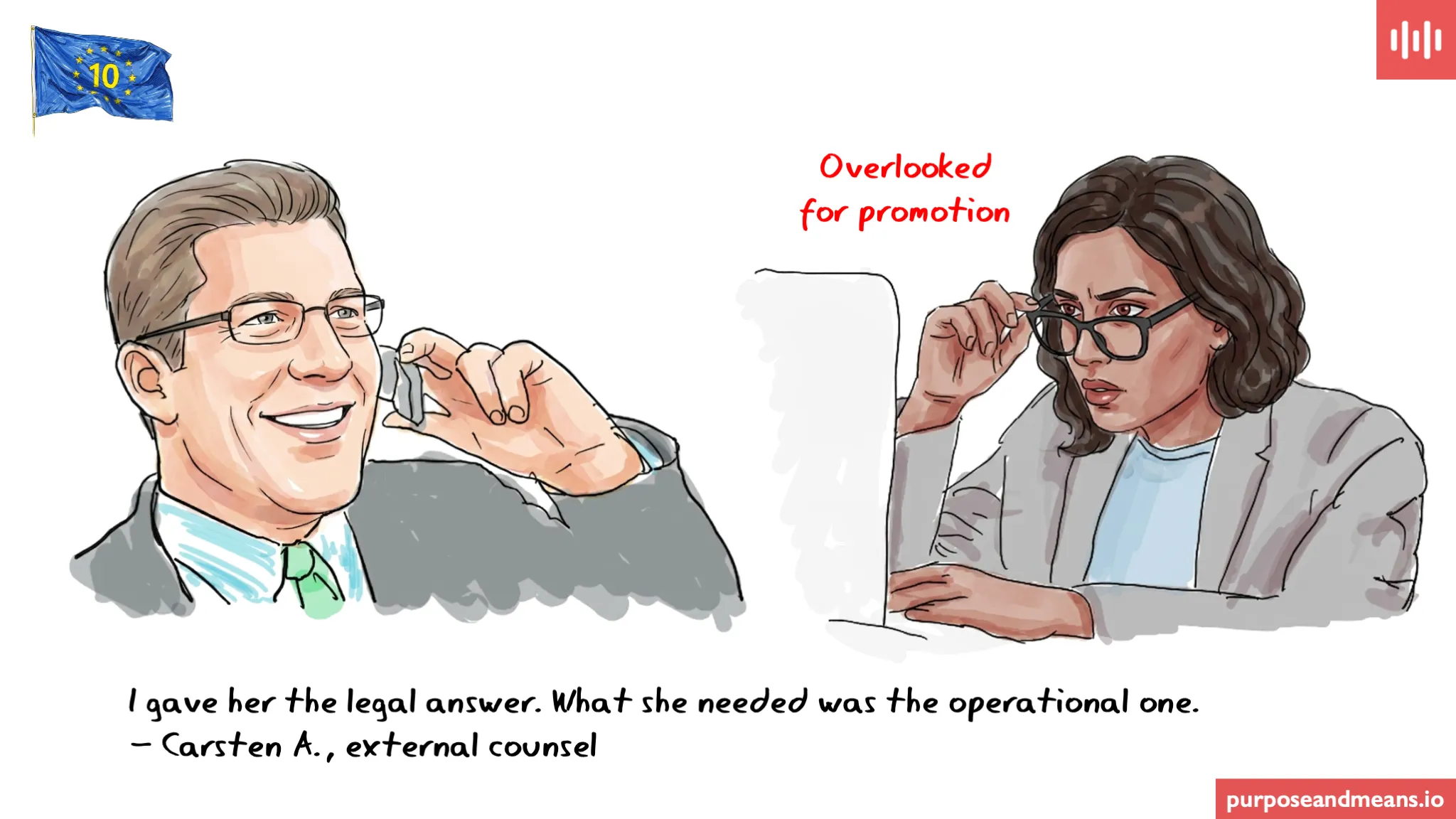
For more on how processor and sub-processor relationships create compliance exposure, see Beyond Legal #24 on what a well-governed Article 28 agreement looks like, and Beyond Legal #29 on what happens when legal advice is not operationally implemented.
Article references: Article 5(2) (accountability), Article 24 (controller responsibilities), Article 25 (data protection by design and by default), Article 28 (processor obligations), Article 28(2) (sub-processor authorisation), Article 28(4) (sub-processor obligations), Article 30 (records of processing activities), Article 83(4) (fines for processor obligation violations), Article 83(5) (fines for infringements of basic principles and controller obligations).
Series: This is post 15 in the Beyond Legal series — 20 roles, 20 days, real consequences. The story about Daan and Carla is fictitious, the Spanish and Italian cases are real.
Purpose and Means works with companies on data protection strategy, governance, and compliance — going beyond the legal text to focus on how things actually get done. If you’d like to discuss what this means for your company, book a call or explore our services.