Data Protection Hero: I have successfully locked my computer when leaving my desk
Locking your computer when you leave your desk is, technically speaking, a data protection control. An unlocked screen, left unattended, is a reasonably straightforward way to give your colleagues access to things they were never meant to see. You have not done that today. This is noted.
#DataProtectionHero
Browse by Topic
access controls
accountability
accountability frameworks
ai act
ai ethics
ai governance
ai infrastructure sovereignty
ai literacy
ai regulation
article 12
article 13
article 22
article 25
article 28
article 30
article 32
article 35
article 46
article 5
article 6
article 7
audit and assessment
automated decision-making
awareness
awareness campaigns
behaviour change
beyond legal
board reporting
case law
change management
cloud infrastructure
compliance monitoring
consent
cookie compliance
cross-border transfers
dark patterns
data accuracy
data breach notification
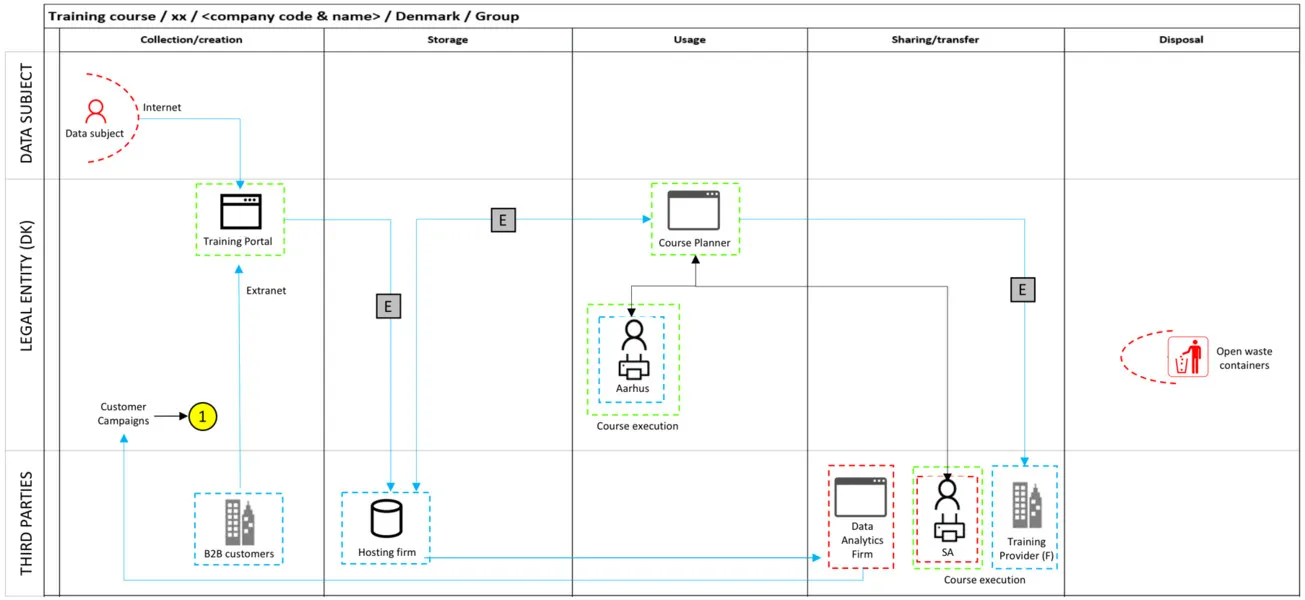
data flows
data mapping
data minimisation
data processing agreements
data protection
data protection by design
data protection day
data protection hero
data protection leader
data quality
data residency
data retention
data science
data sovereignty
data subject rights
datatilsynet
deceptive design
direct marketing
dora
dpia
education
employee data
employee engagement
eprivacy
esg
executive communication
external legal counsel
finance and banking
gdpr
gdpr at 10
generative ai
governance
grc
healthcare
horizon scanning
hr and data protection
hr and employment
incident response
information security
intellectual property
internal communications
international transfers
lawful basis
leadership
lego serious play
machine learning
marketing
nis2
privacy by design
privacy culture
product management
profiling
public sector
purpose limitation
quantum computing
records of processing
regulatory guidance
risk management
risk reduction
ropa
sales
security
software development
special category data
standard contractual clauses
strategic planning
sub-processors
supply chain
sustainability
third-party risk
training design
transparency
trend radar
ux design
vendor management
visual communication
weak signals
workshop facilitation