GDPR: which tool to use for mapping data flows
Note: I wrote this article in March 2016. You may find the article and comments interesting, but for a more updated view and a useful template I suggest you read my later article, GDPR data flow mapping — an approach.
Which tools can organisations use to map personal data flows for GDPR? #
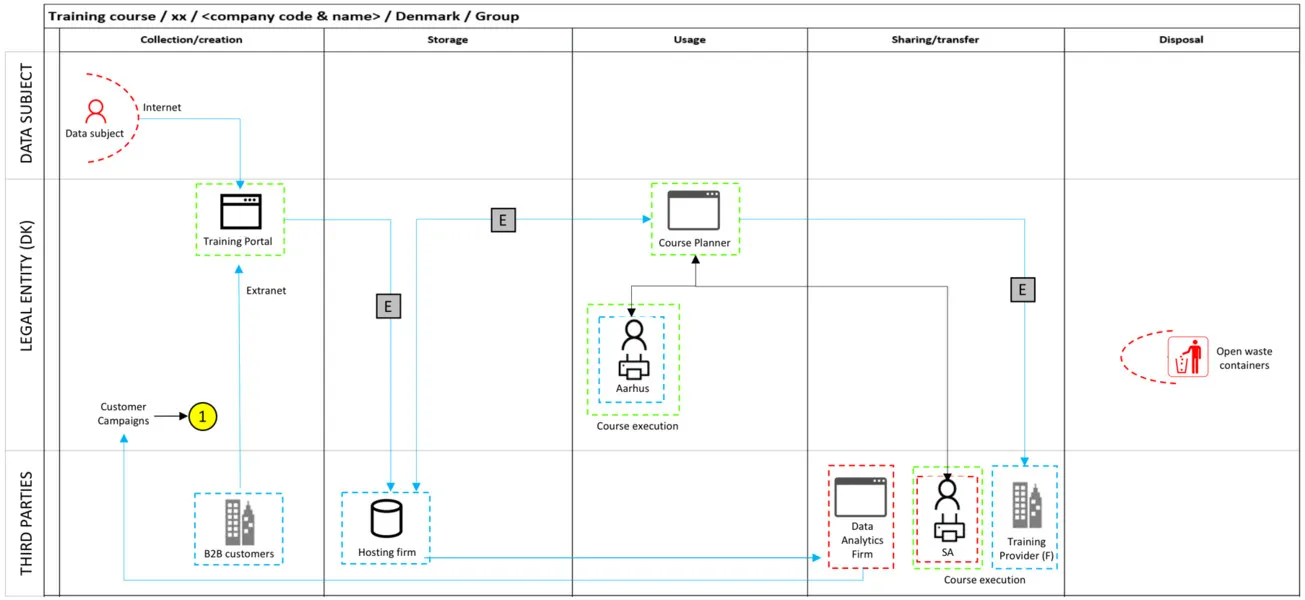
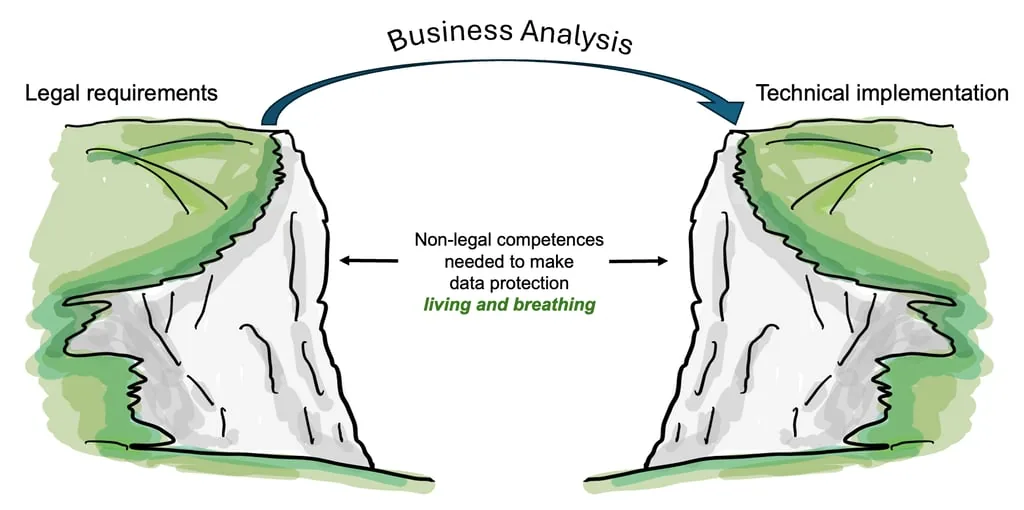
Organisations approaching data flow mapping for GDPR have a wide range of options — from general-purpose tools such as Visio, PowerPoint, Excel and Word, to enterprise architecture platforms such as ARIS, to dedicated Data Protection Management System tools that include data flow mapping functionality. The right choice depends on the scale of the organisation, the complexity of its processing activities, and whether the tool can support ongoing maintenance of the data inventory after the initial project is complete. At the time of writing, one tool worth investigating is Microsoft’s free Threat Modelling Tool, designed for data flow mapping and threat analysis.
Elements of Article 30 — records of processing activities — point to the need for organisations to map data flows for personal data, including sensitive personal data and identity data. Many may reach for Visio, PowerPoint, Excel or Word, and some may even use the back of a fag packet. Large organisations may already have enterprise tools such as ARIS that could be fit for the purpose.
Although Data Protection Management System tools are emerging that may include data flow mapping functionality, I am curious to know how other organisations intend to tackle this significant task within their GDPR project — and, beyond the project, how they intend to maintain the personal data inventory on an ongoing basis.
Is Microsoft’s Threat Modelling Tool worth considering for GDPR data flow mapping? #
Microsoft’s Threat Modelling Tool supports their own Security Development Lifecycle (SDL Practice #7) and has capable functionality for data flow mapping, understanding threats, and documenting countermeasures. It is based around the STRIDE threat classification, which does not specifically cover all data protection threats — though this is not a significant obstacle when adapting it for GDPR purposes. A further advantage is that the tool is free. It has been available for several years, with a 2016 version available at the time of writing, which gives it reasonable longevity. An informative video is available that explains the modelling concept and the tool in detail.
A question for practitioners #
How is your organisation approaching data flow mapping for GDPR? And what plans are in place to maintain the personal data inventory after the project closes?
I would be genuinely interested to hear what others are doing.
I help data protection leaders assess and improve their data protection programme capability. If you would like to discuss this in more detail, book a call or explore our services.